Block Emails or Files including archives or Social Posts using Keywords
Overview
When any employee/user from your network leaked the confidential information intentionally or unintentionally, then what will happen? Huge loss to your organization.
In your organization various mediums and modes comes into play for data leakage. Users can upload important document to internet, even though your content filtering software does not allow users to upload Microsoft Word and Microsoft XL files, users can act smart and creates an archive using those files and tries to upload achieved files. Some times policy in your organization is to not block archive files since network administrator/ manager uses archive files to transfer log files of large sizes.
Your company has a plan for protecting data from external intruders, but does not protect against theft and accidental disclosure of sensitive information by employees and partners. These employees and partners may simply take information out of Microsoft Word and Microsoft XL files and simply send an Email to third party.
In modern era, these kind of data leaks are become a challenge for organizations. Organizations are in a quest for content filtering software’s which can deeply inspect archive files and able to identify whether the archive or emails contains any confidential details of organization. Most of such archive files and emails have important keywords that should be matched while tracing the Data Leakage.
This challenge is also big for security experts because when there is an upload the post data formation is different for Gmail / Google Drive/ Media fire/ Drobox etc. The wide range of formations of post data made it difficult for security experts to derive concrete solution to these challenges.
To overcome such problems SafeSquid comes up with Advanced DLP solution embedded into SafeSquid SWG, which analyzes post data, deeply inspect archives files using file decomposition method and can identify whether any archive file or emails or social media post contains certain keyword matches. Based on the matched keyword your network administrator can take effective actions like block upload if user name is XYZ or block the data transfer if the destination website is say www.abcd.com.
The Advanced DLP solution can be managed from SafeSquid Self Service portal from where you can create various keyword expression matches. SafeSquid SWG will download those keyword expressions and loads into memory. When any user try to upload any archive file or write an email, SafeSquid SWG will analyze Post data and transmit it to the ClamAV daemon for Signatures verification. If the keyword expression matches with your email or file content then ClamAV daemon responds. SafeSquid will further take respective action based on policy you have created for those keywords matching.
Manage Keyword Signatures using Self Service portal
Configure SafeSquid SWG for using Custom Signatures
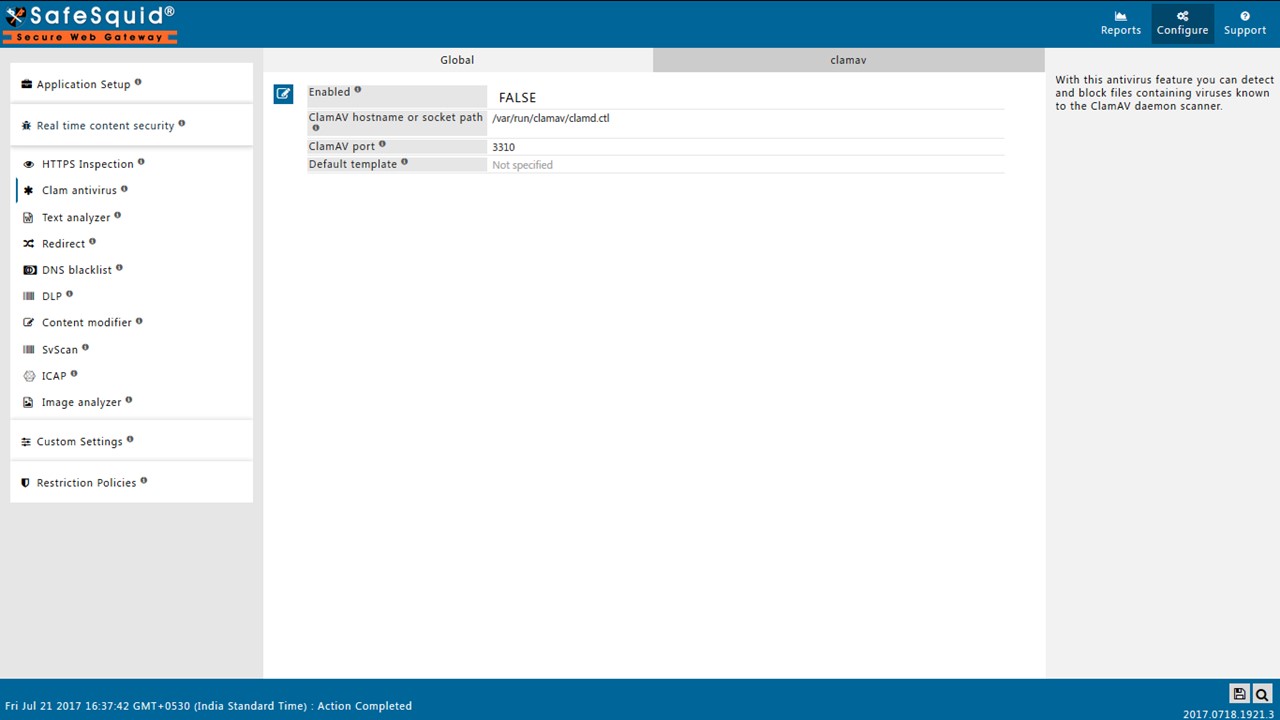
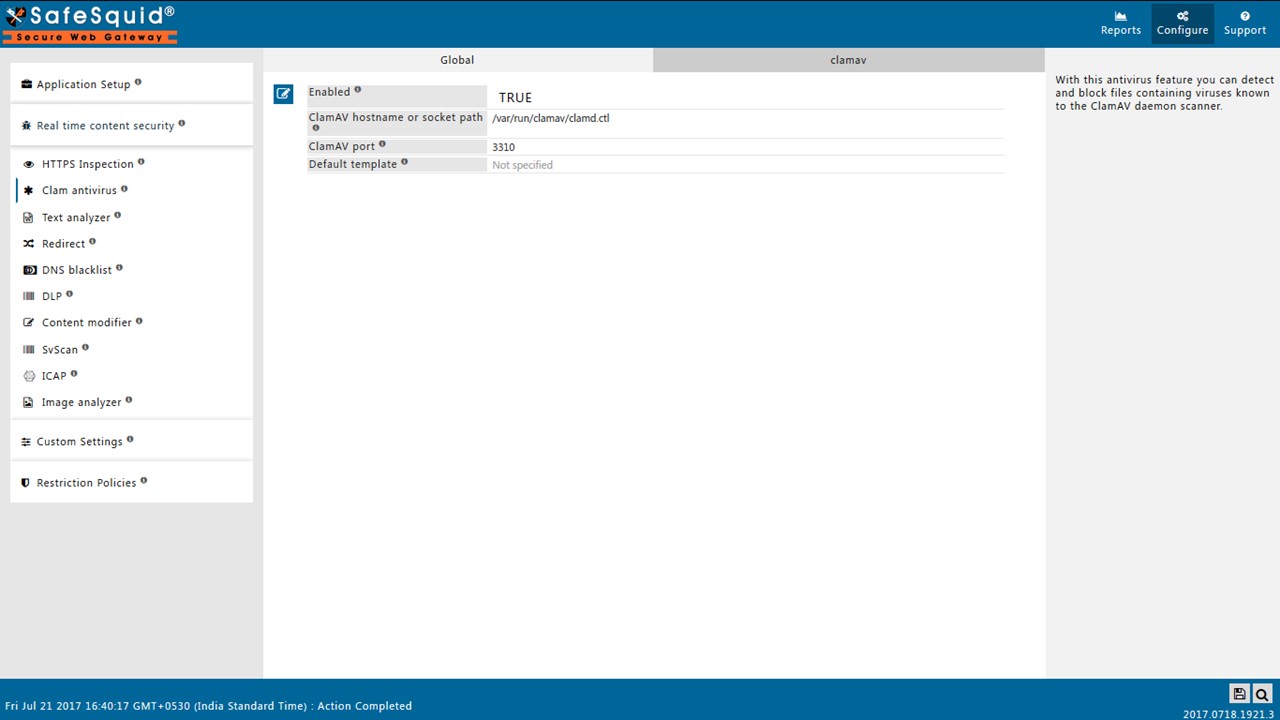
On configure page of SafeSquid interface open the Real time content security side menu. Click on Clam anitivirus section to configure the policy.
Click on Global part of ClamAV Section and make Enabled as True.
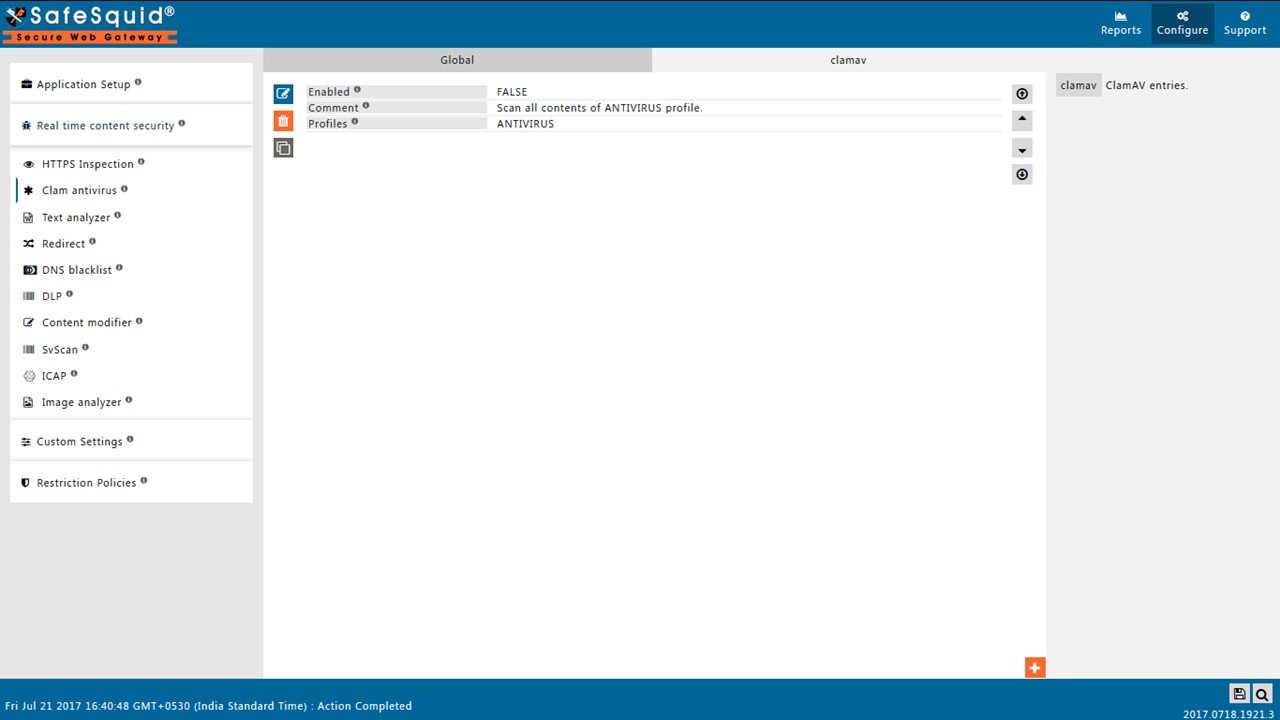
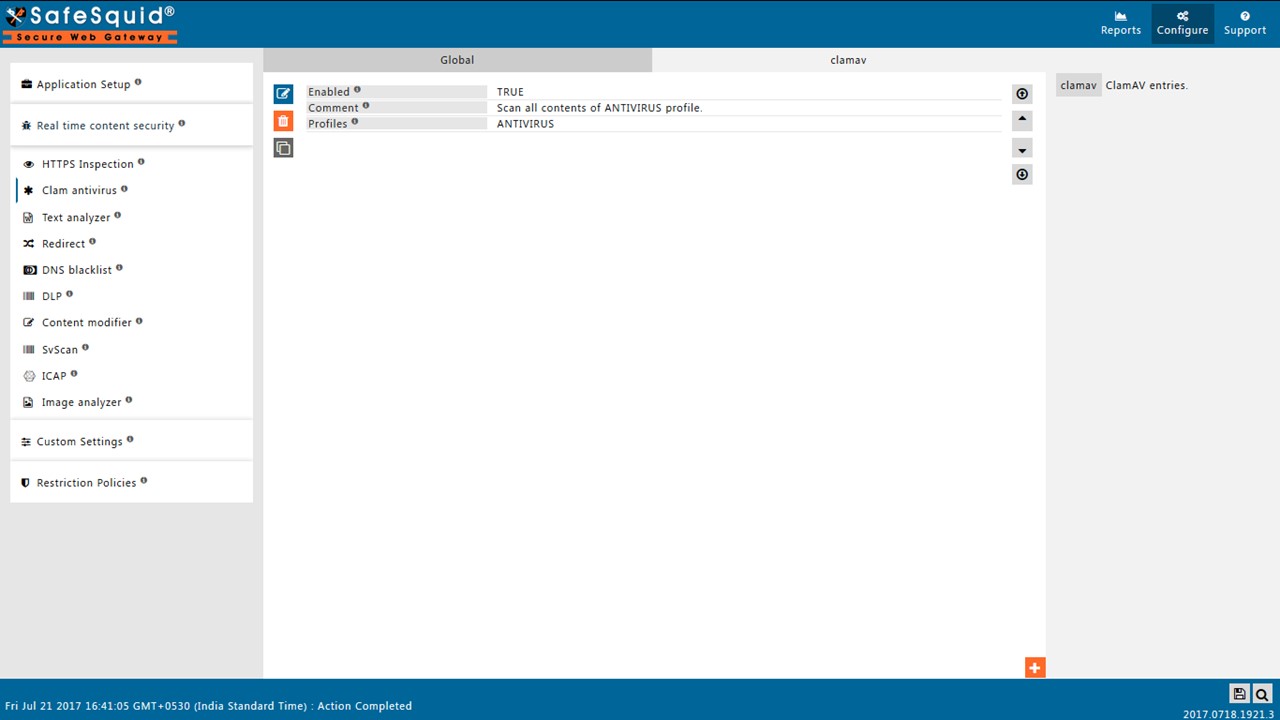
Now click on clamav subsection to configure the policy.
Enable the default policy in the subsection for virus signature detection.
Your policy will be as shown below.
Click on bottom left Icon to save the configuration.
Note : Once you configured the policy as shown above go to Support page and Click on Refresh button for refreshing subscription details.
Testing Signature detection
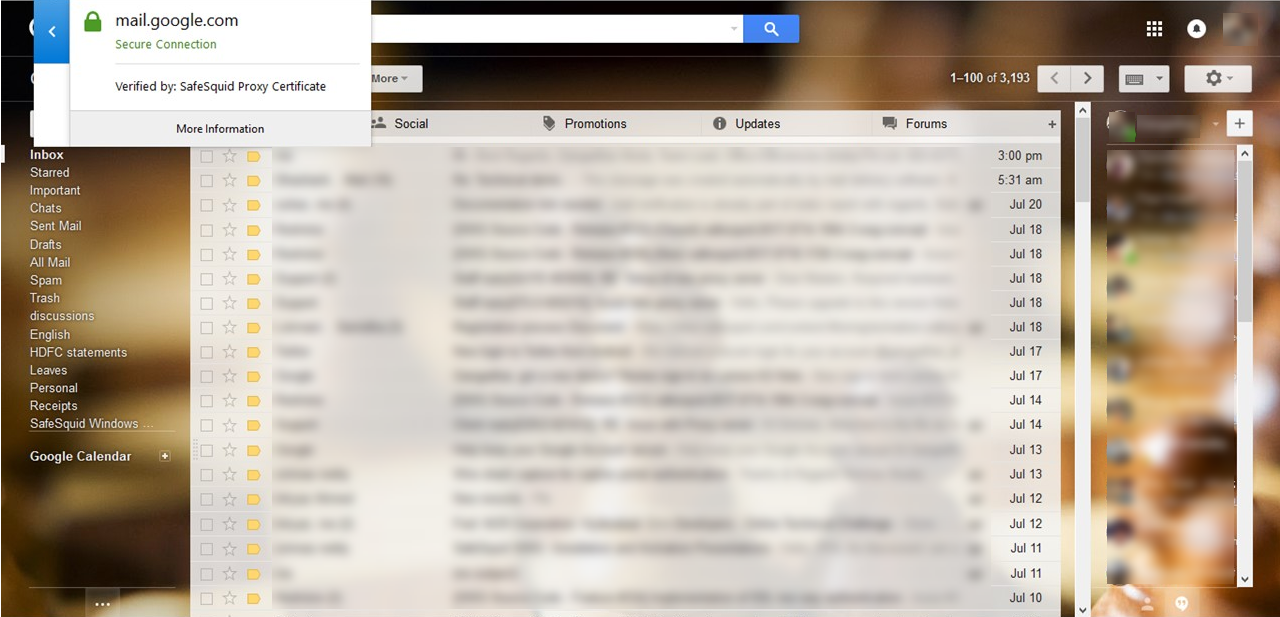
HTTPS Inspection should be enabled in SafeSquid. If not enabled, you can check our document - How To Enable HTTPS Inspection
Test using office documents
Set proxy settings in client browser and open Gmail. Confirm the HTTPS traffic is verified/inspected by SafeSquid. Otherwise SafeSquid will not be able to block the mail which contains your mentioned keyword(s).
Create a dummy Microsoft file and include your set of keywords into it. Also prepare a separate archive file to test the scenario.
Now try to attach your sample Microsoft file into mail. SafeSquid Should be able to block your attachment.
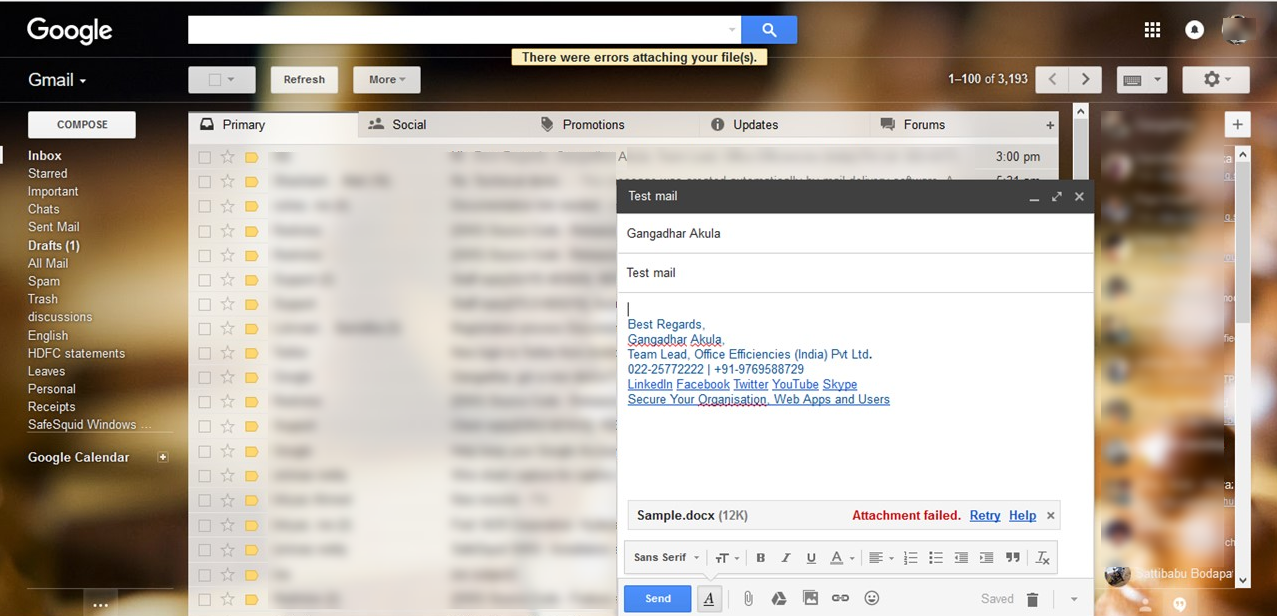
That's it. Your created signatures are in the action and your data is safe.
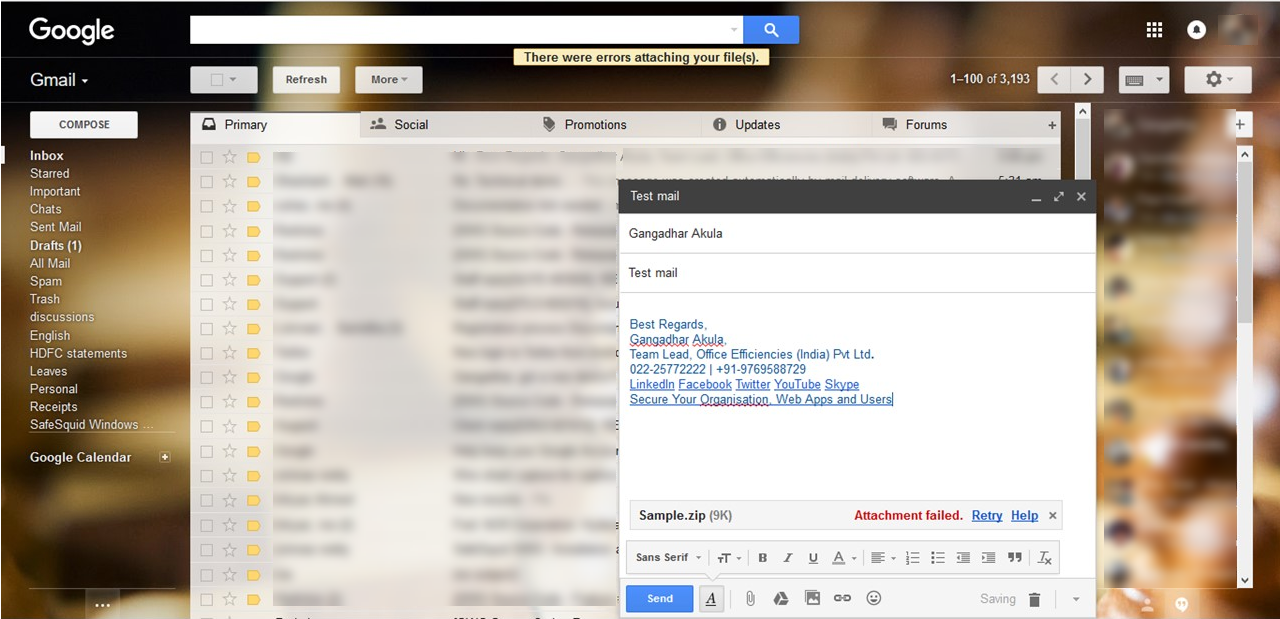
Test using archive files
Now try to attach your archive file into your mail and you should see that archive file is also blocked by SafeSquid.
Test using emails
Create an email draft using set of keywords for which you have created signatures.
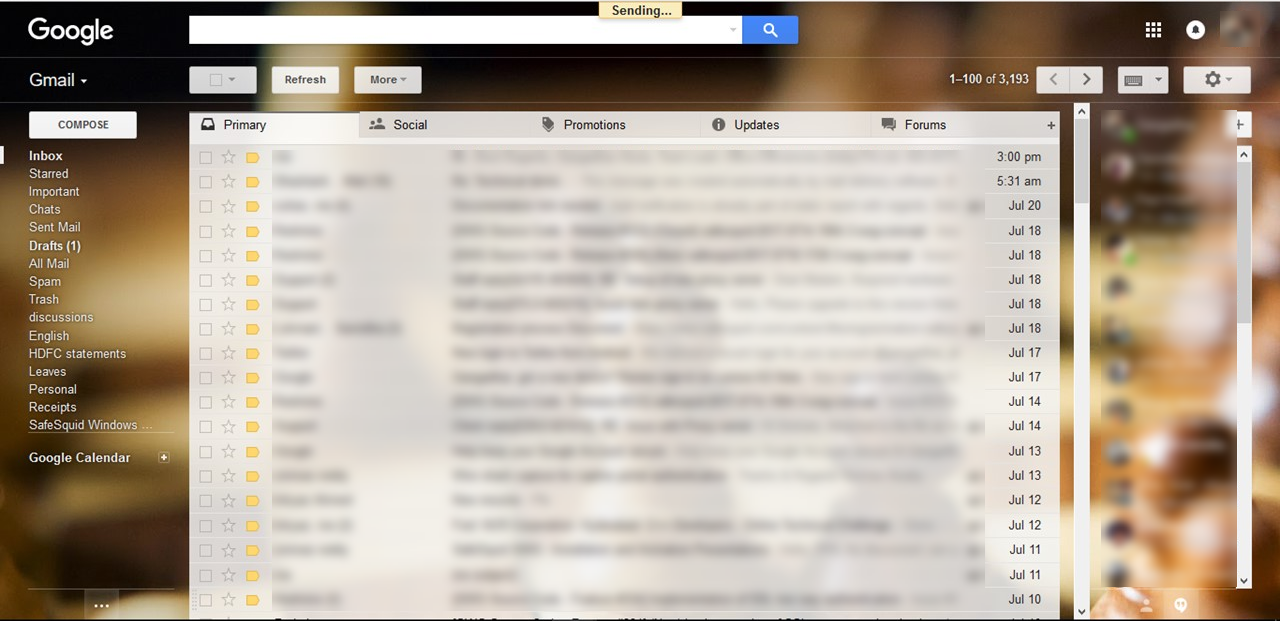
Before sending the mail SafeSquid will identify the keywords and will block the mail. You can see that Save Failed in gmail compose box.
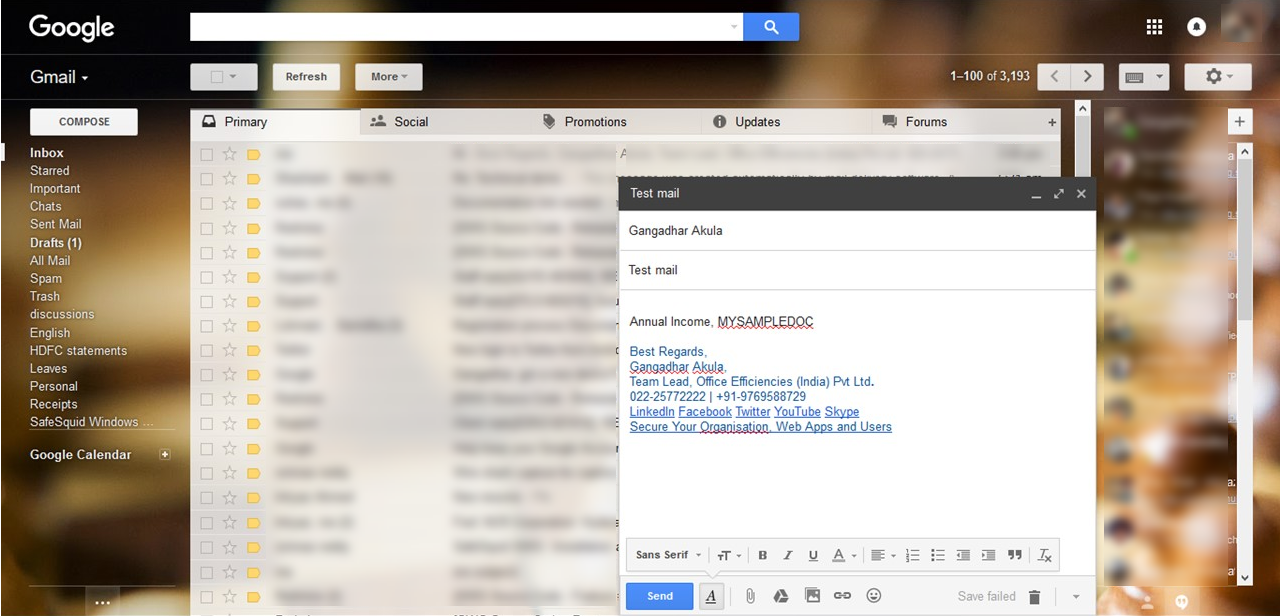
You can observe on your browser, when you click on send button, then the mail will be kept on trying to send the mail.
Test using social media posts
Open www.facebook.com and login with your credentials.
Now try to post a status update using your keywords. When you click on submit button, you will not see your post on facebook page.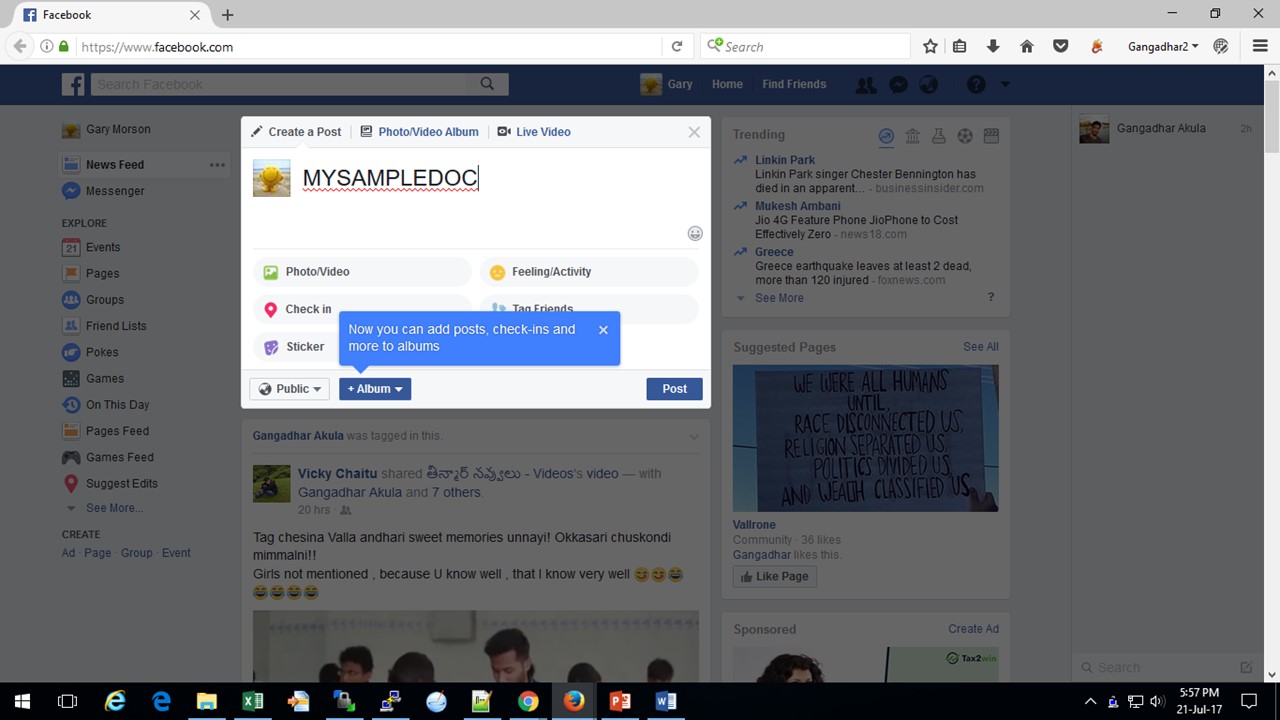
Even if you try to post the same from your timeline you will not be able to post your status with the specified keywords.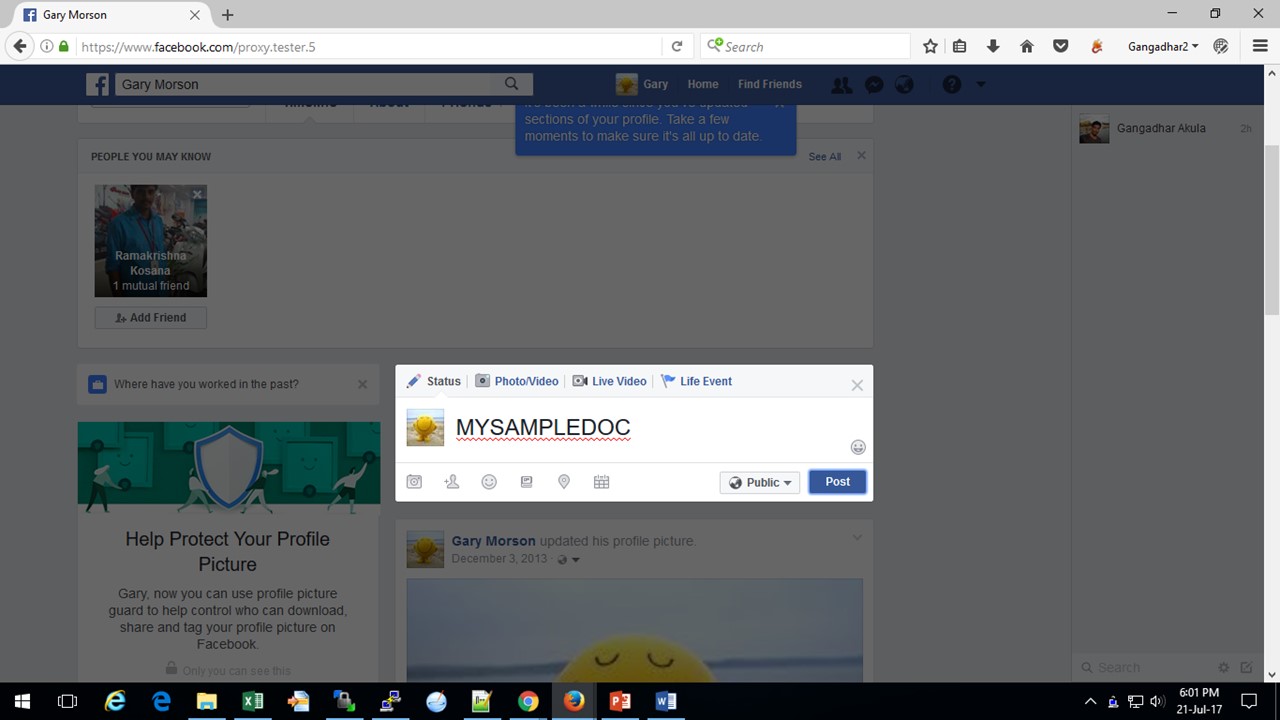
Now try to post the comment, you will not be able to post any comments with those specified keywords.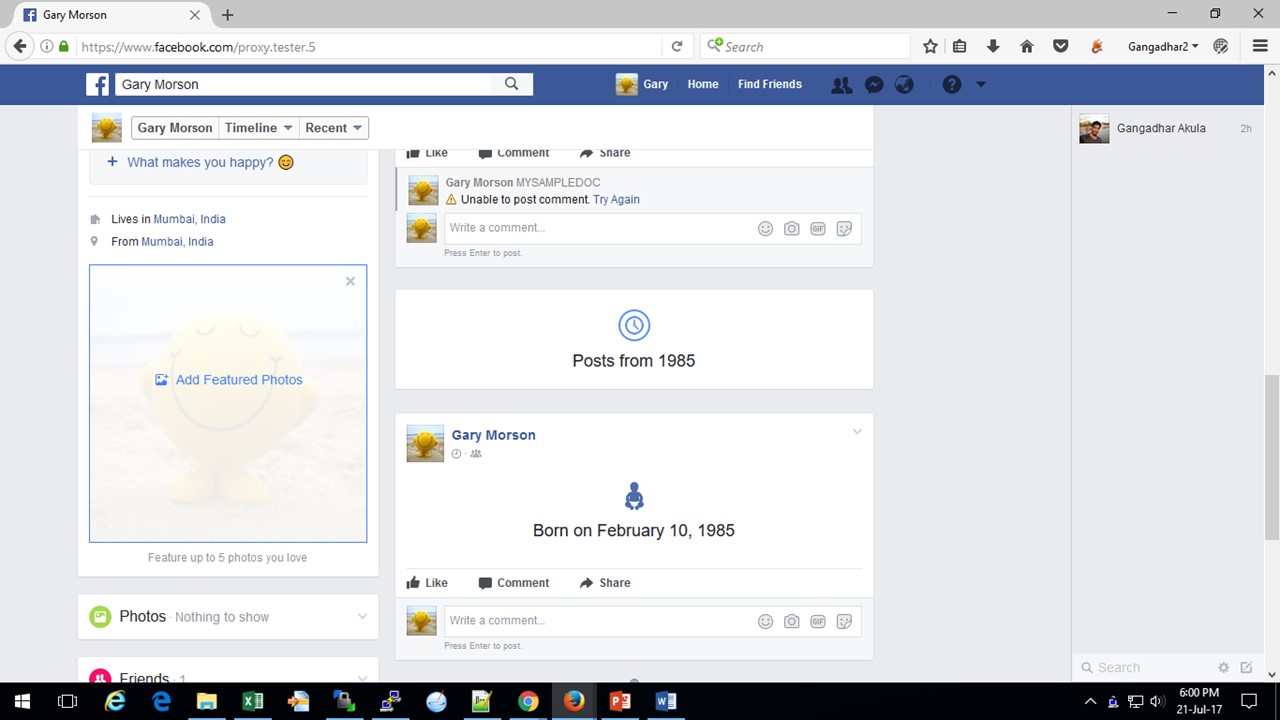
You can perform same tests with any of the website by posting data with your specified keywords. You will not be able to post any important information having the keywords mentioned.
Troubleshooting
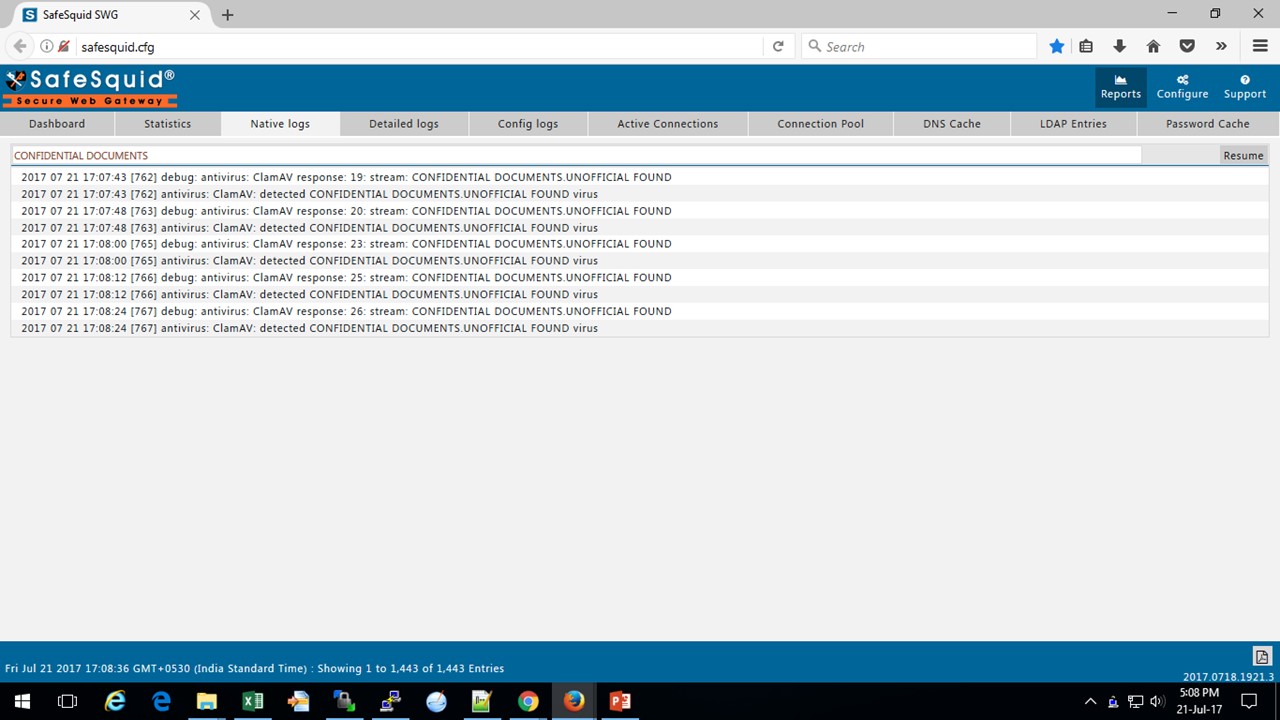
Check SafeSquid logs
You can check SafeSquid logs for troubleshooting, if things are not working as explained above.
Check ClamAV daemon Status
You can check whether ClamAV daemon is running or not using following command.
netstat -lnp | grep clamd
If you found that ClamAV daemon is not running then restart using following command.
/etc/init.d/clamav-daemon restart
Check Signatures File
If ClamAV service is running then check whether you have signatures database file on disk or not using locate command.
updatedb && locate safesquid.ldb
/var/lib/clamav/safesquid.ldb
/var/lib/safesquid/content_signatures/safesquid.ldb
Check ANTIVIRUS profiles applicability.
If you still got any problem you can send us mail at support@safesquid.net