HTTPS Inspection
Overview
This section allows you to configure the overall operation to handle scanning of connections under HTTPS (HTTP over SSL).
SSL (Secure Sockets Layer), is the standard security technology for encrypting a connection between a web server and a browser.
Once established, this connection will encrypt all traffic and ensure that all data passed between the web server and browser remains private
You must set this carefully, depending on the usage of web applications handling HTTPS requests, particularly web 2.0 applications.
All HTTPS requests are matched with the rules defined under the HTTPS scanning policies and actions taken based on the matching entry.
Prerequisites
Generate SSL certificates from self service portal
First you have to generate SSL certificates from self-service portal before configuring HTTPS inspection.
Setup your SSL certificates from self-service portal
Download SSL Certificate from SafeSquid User Interface
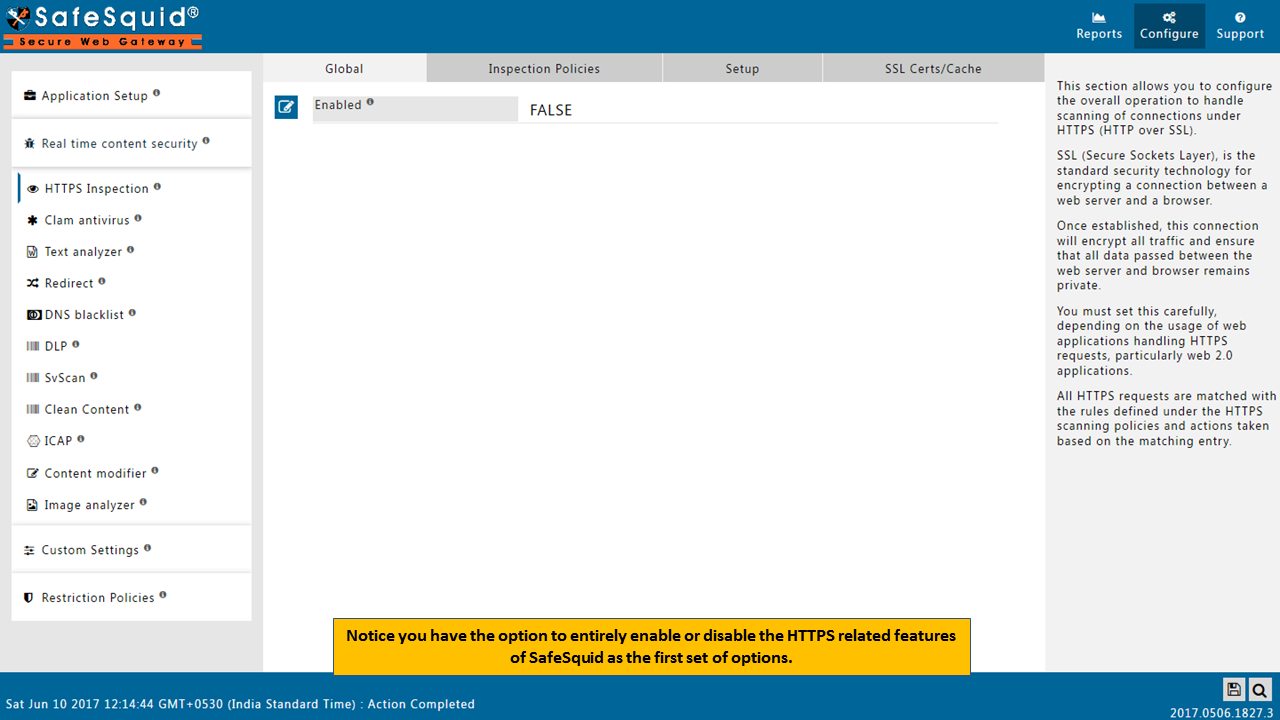
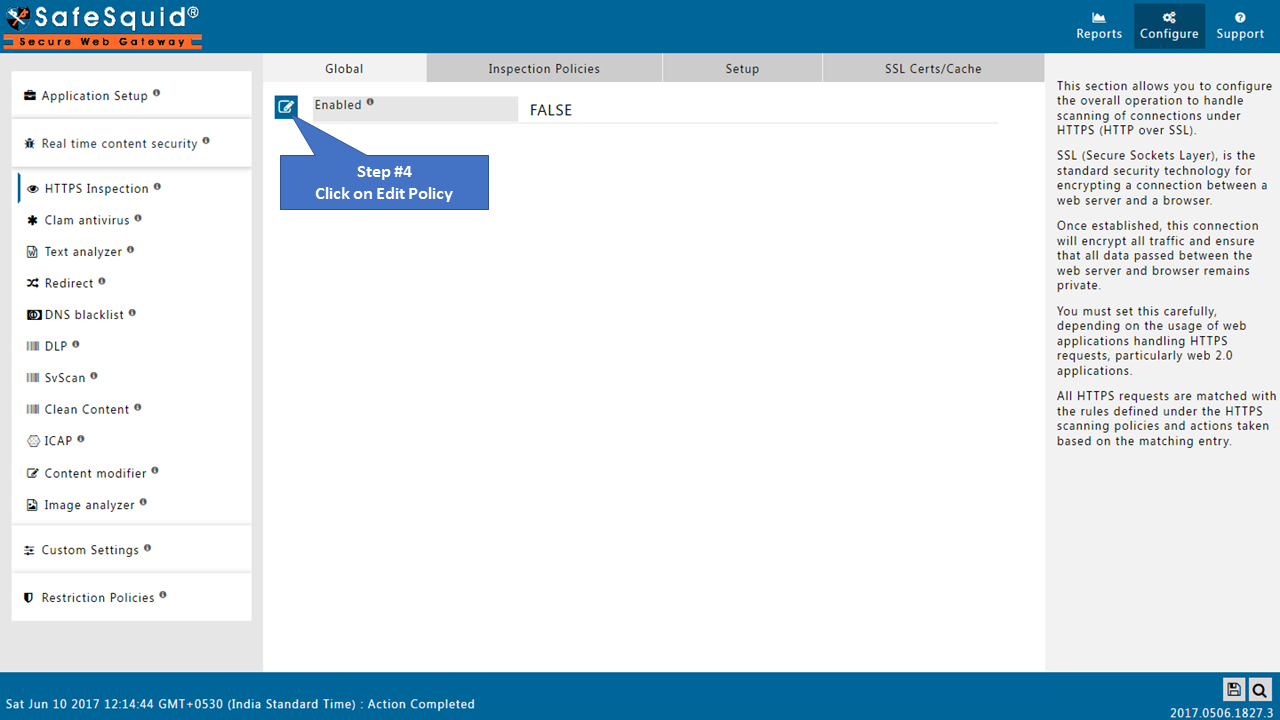
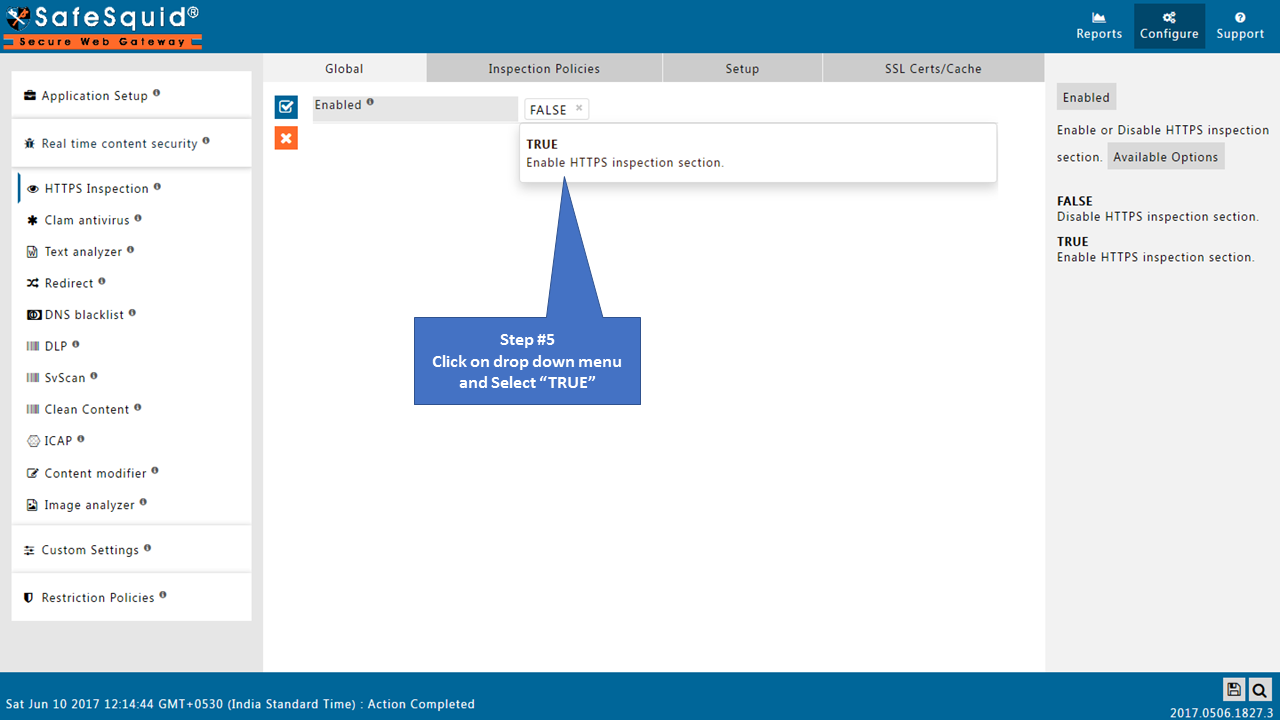
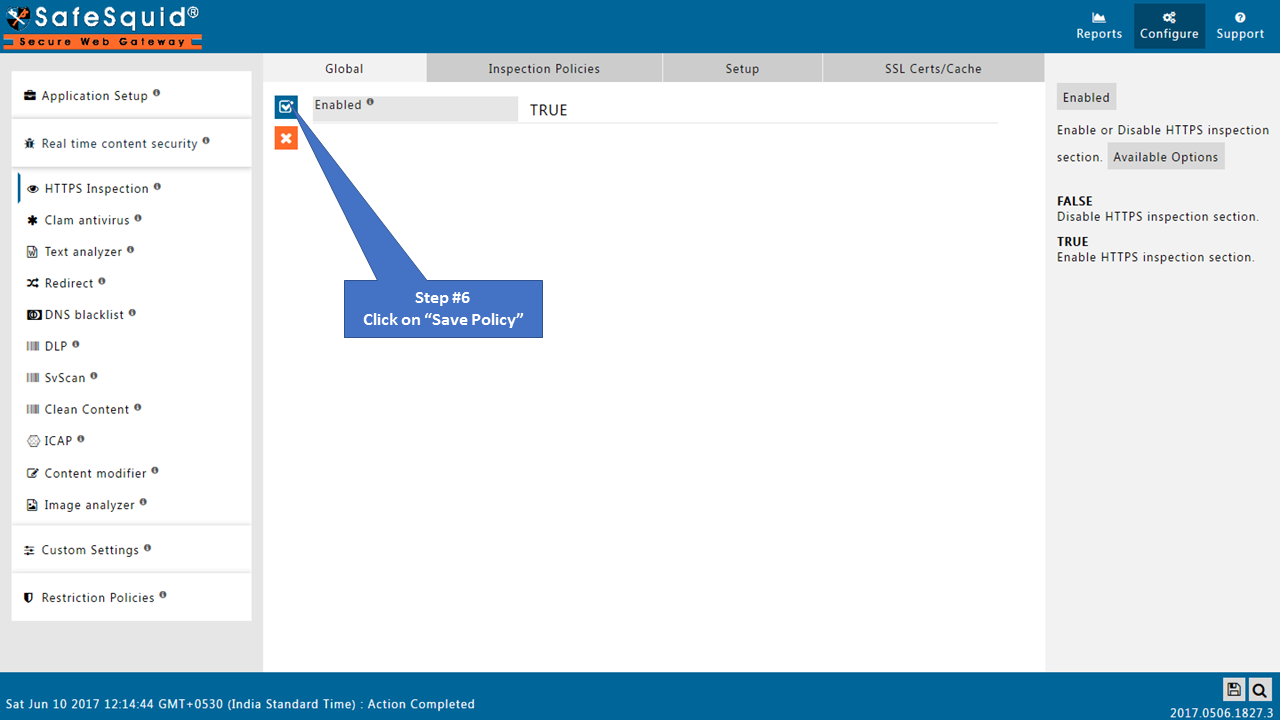
Enabling HTTPS inspection on SafeSquid User Interface
Access the SafeSquid interface
Go to Configure Page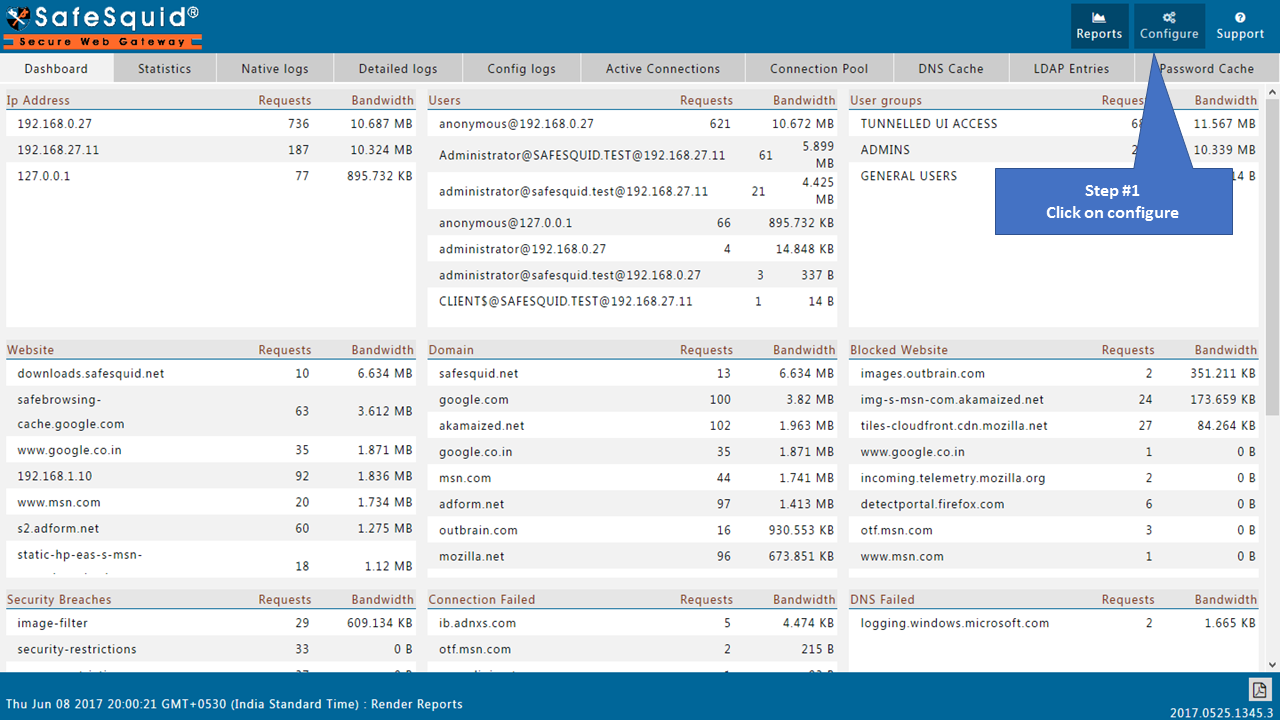 |
|
Go to Real time content security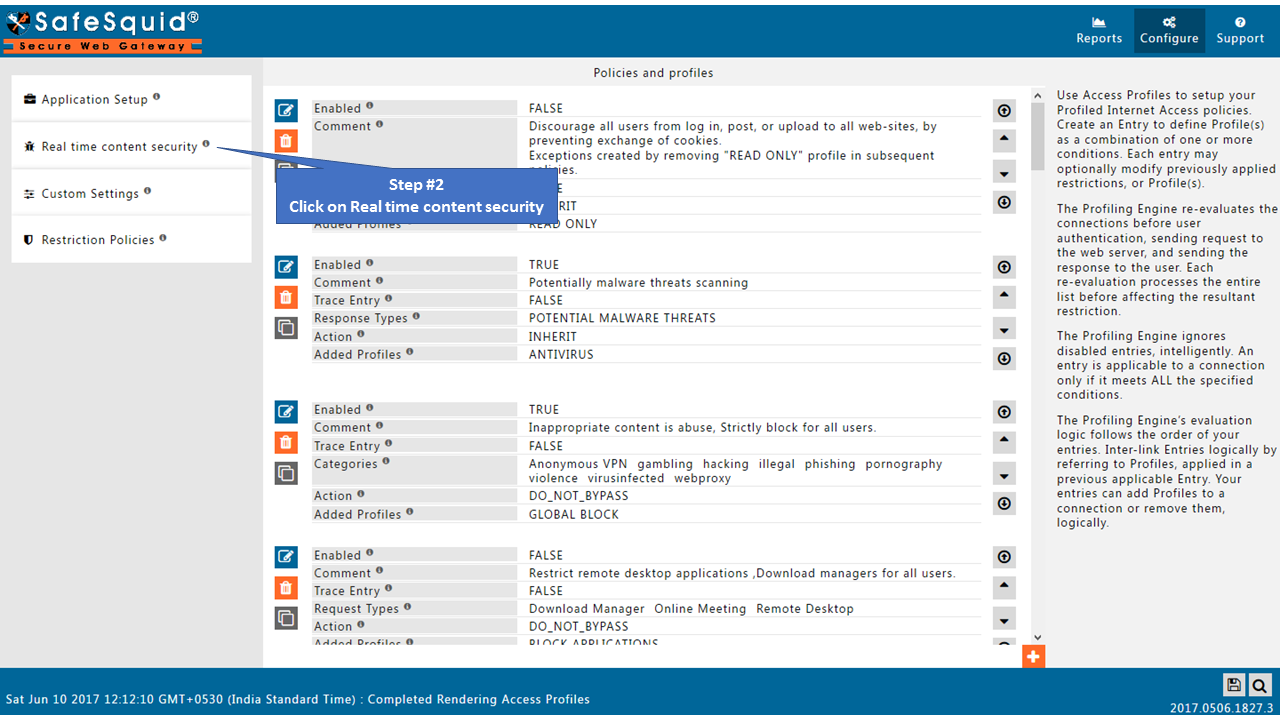 |
|
Go to HTTPS Inspection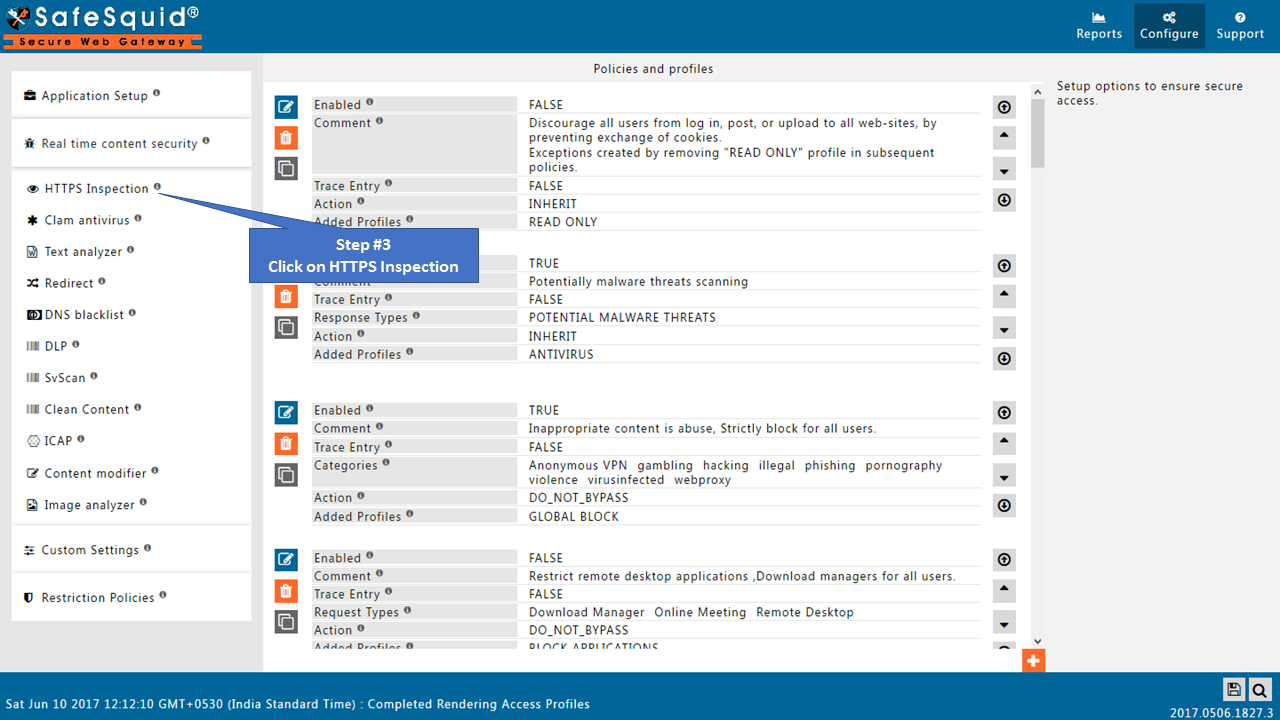
|
|
GlobalEnabledEnable or Disable this section.
 |
|
 |
|
 |
|
 |
|
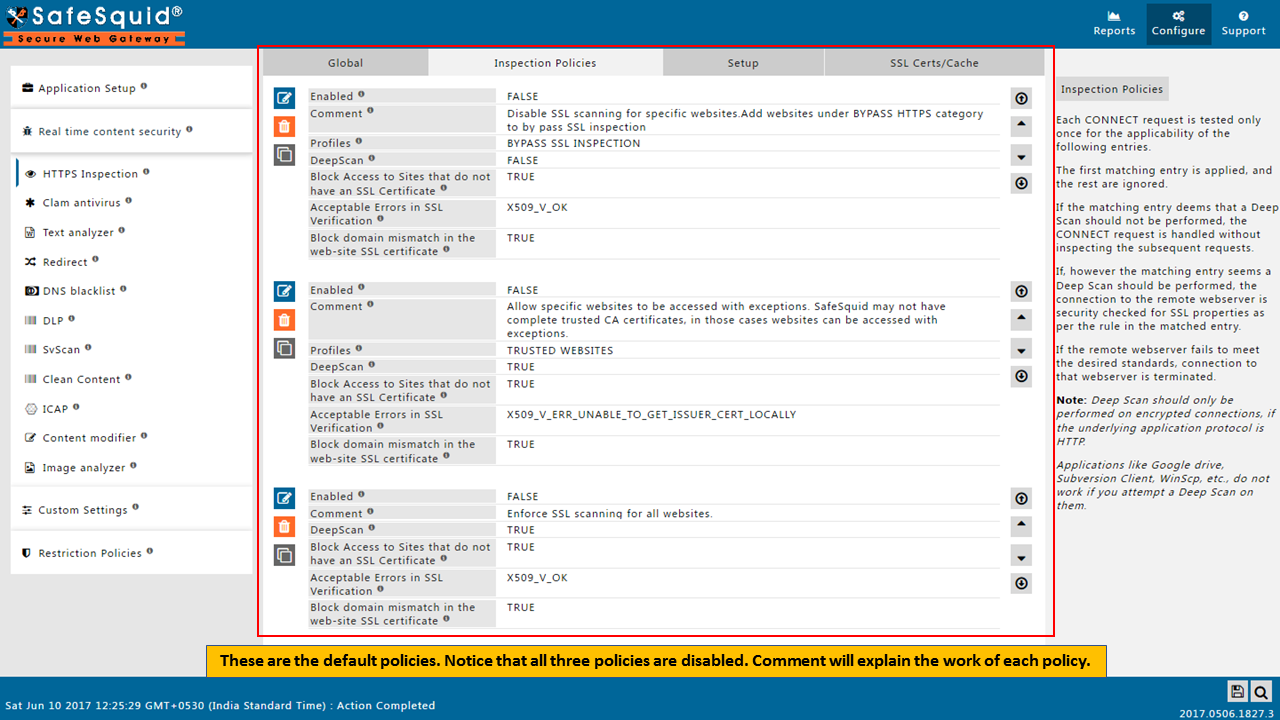
Inspection PoliciesEach CONNECT request is testedonly once for the applicability of the following entries. The first matching entry is applied, and the rest are ignored. If the matching entry deems that a DeepScan should not be performed, the CONNECT request is handled WITHOUT inspecting the subsequent requests. If, however the matching entry deems a DeepScan should be performed, the connection to the remote webserver is security checked for SSL properties as per the rule in the matched entry. If the remote webserver fails to meet the desired standards, connection to that webserver is terminated. Note: DeepScan should only be performed on encrypted connections, if the underlying application protocol is HTTP. Applications like Google drive, Subversion Client, WinScp etc., do not work if you attempt a DeepScan on them. 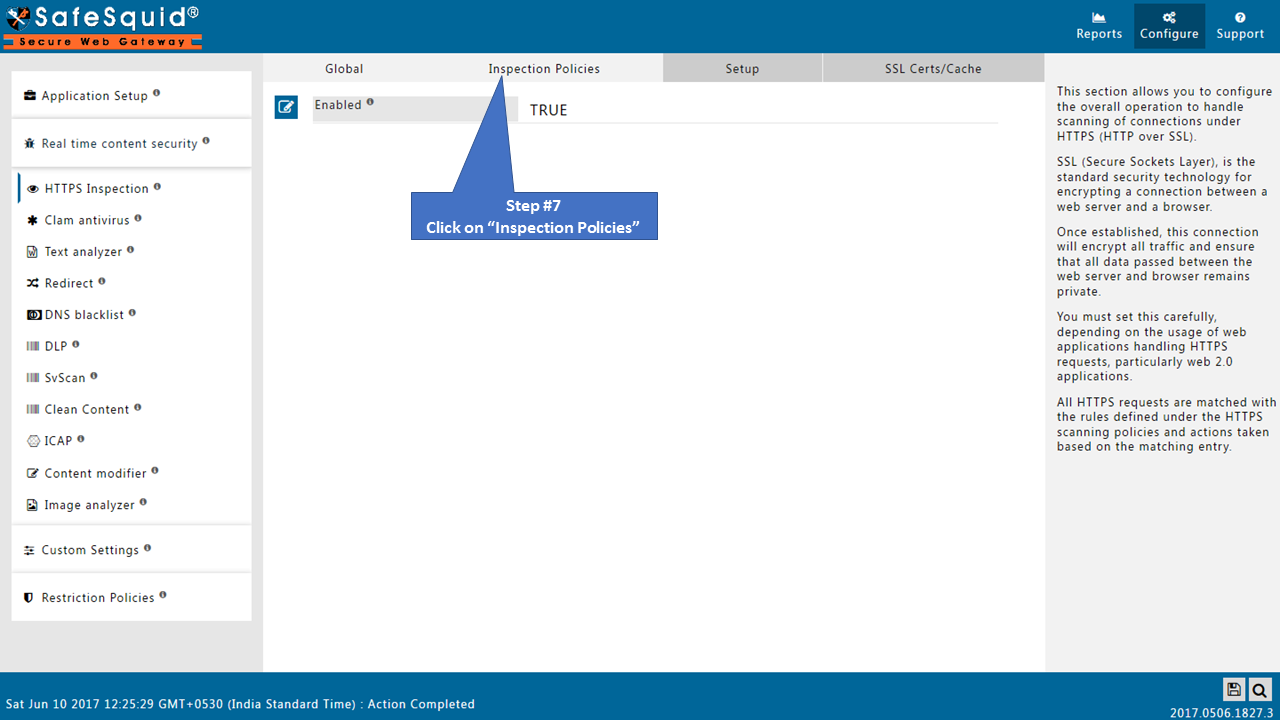 |
 |
|
|
SafeSquid comes with some default Inspection policies as follows
Enable or Disable above policies as per the requirement or add new policy for new requirement EnabledEnable or Disable this entry
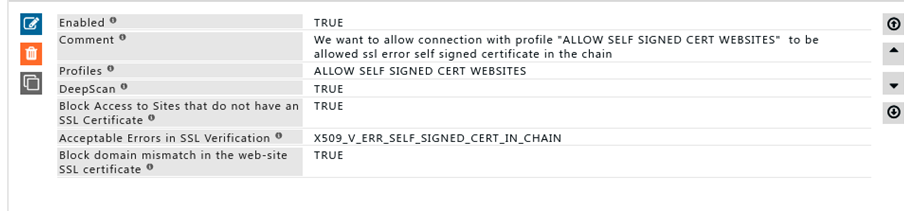
CommentFor documentation, and future references, explain the relevance of this entry with your policies. That is, by reading the policies, a future user can understand the purpose of that entry. ProfilesSpecify the Profiles applicable for this entry. This entry will be applicable only if the connection has any one of the specified profiles. Leave it Blank, to apply for all connections irrespective of any applied profile. To avoid application to a connection that has a profile, use negated profile (!profile). DeepScanDecide if you want to enable scanning within encrypted SSL connections matching this entry.
Block Access to Sites which do not have an SSL CertificateDecide whether Sites that do not have SSL Certificate should be blocked or not.
Acceptable Errors in SSL VerificationSafeSquid verifies the SSL certificate to remote SSL web-servers. You can specify here, the acceptable level of error. Only in specific or exceptional cases choose anything besides X509_V_OK. Block domain mismatch in the web-site SSL certificateDecide whether domain name mismatch is to be allowed or not. SafeSquid validates the DNS and Common Name in the SSL certificates supplied by the remote web-server. Only in exceptional cases set this as FALSE.
|
|
ExampleRule#1 I want to allow websites which are self-hosted with self-signed certificates Connection with profile “ALLOW SELF SIGNED CERT WEBSITES” will bypass SSL error ERR_SELF_SIGNED_CERT_IN_CHAIN Save Configuration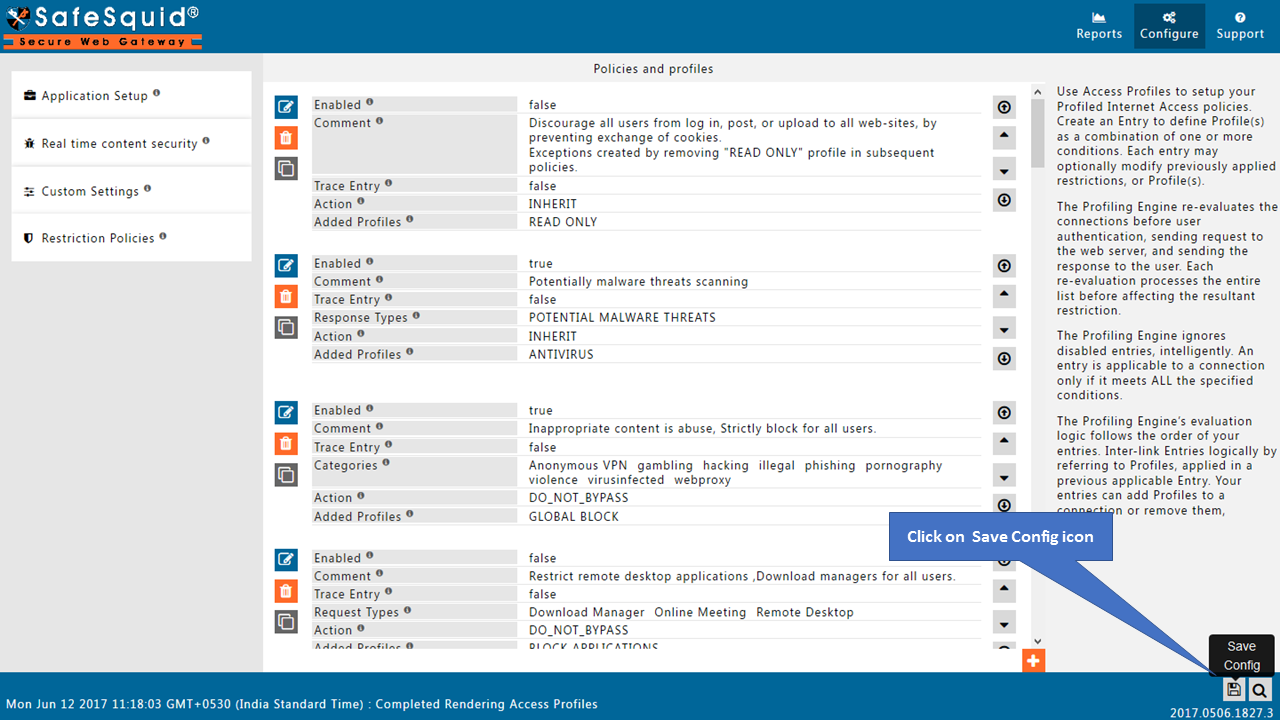 |
|
No configuration required in Setup tabNote : In new versions of SafeSquid released after June-2017, setup tab is removed. You will see only three subsections in HTTPS inspection section. SetupList of Security Passphrase(s) or Server Policies required to generate or load an existing ROOT CA SSL Certificate (RCSC). The first matching entry below is used and the remaining is ignored. RCSC is automatically created if none exists already. If an RCSC exists, passphrase in the applicable entry is used to load it. The Private key of the generated RCSC can be used only with the passphrase used to generate it. The passphrase prevents the private key of your RCSC from being stolen or fraudulent use. After the RCSC has been successfully generated, the public key of your RCSC can be downloaded from http://safesquid.cfg/safesquid.cer The public key must be installed on all the Web-Clients and browsers that are subjected to Deep Scan. Click on Add below, to add a new entry. 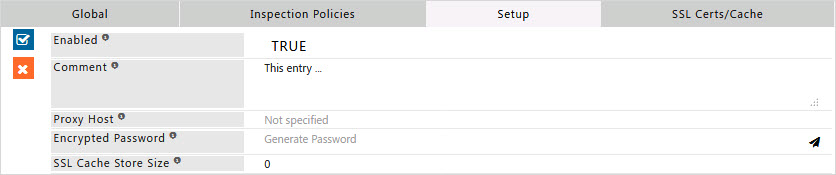
EnabledEnable or Disable this entry
CommentFor documentation, and future references, explainthe relevance of this entry with your policies. Proxy HostPlease enter the host name of the proxy server as specified in the Startup Parameters. Encrypted PasswordPlease enter the Encrypted password for disk based caching of SSL certificates. |
|
Generate SSL certificates from self service portalFirst you have to generate SSL certificates from self-service portal before configuring HTTPS inspection. |
|
Setup your SSL certificates from self-service portal |
|
SSL Certs/CacheDownload SSL Certificate from SafeSquid User InterfaceDownload : Download the SafeSquid certificate. Upload : Upload the SafeSquid Certificate. Cache Refresh : Refresh the cache. |
|
Importing SafeSquid SSL certificate into your browserInstall SafeSquid SSL certificates into the browsers. If you did not install certificate into the browser and HTTPS inspection is enabled, then you will get an error while accessing the HTTPS websites. |
|
Importing into Mozilla FirefoxImporting into Internet Explorer Or Chrome Browser |
Having HTTPS inspection feature some interesting things that you can do with this SafeSquid SWG
- Block access to consumer Google accounts
- Give Read only access to the Facebook, Twitter sites. Users can able to login into their accounts but they cannot able to do post or comment or like or chat.
- Enforce safe search or safety mode based searches in Google, Bing and Yahoo search engines and also, we can enforce in any websites that are offering safety mode based search.
- Block images over Google
- Filter text, Images over HTTP and HTTPS sites
- Allow specified users to access or to login into specified HTTP and HTTPS sites and block others
- Can use Virus scanning for both HTTP and HTTPS sites?
- Blocking attachments to Gmail and Block Gmail Chat